How do vishing scams work, how do they impact businesses and individuals, and how can you protect yourself, your family and your business?
We’ve all heard of phishing, the tried-and-tested email scam that spoofs authoritative sources to trick recipients into handing over sensitive information or downloading malware. Well, vishing is its voice call equivalent. It’s a con trick with many variants that can impact individuals and organizations alike – with potentially devastating consequences.
Together phishing, smishing, pharming and vishing cost more than 241,000 victims over $54 million in 2020. And that’s just the cases that were reported to the FBI as many cases of fraud go unreported.
So how do vishing scams work, how do they impact businesses and individuals, and how can you protect yourself from them?
The problem with social engineering
Vishing works across the consumer and business sphere for one very good reason: human fallibility. Social engineering lies at the heart of the bad guys’ efforts. It is, in effect, the art of persuasion. Social engineering is about impersonating a trusted authority – your bank, technology provider, the government, an IT helpdesk worker – and creating a sense of urgency or fear that overrides any natural caution or suspicion the victim may have.
RELATED READING: Would you take the bait? Take our phishing quiz to find out!
These techniques are used in phishing emails and fake text messages (known as smishing). But perhaps they’re most effective when used “live” over the phone. Vishers have several additional tools and tactics to make their scams more successful, including:
- Caller ID spoofing tools, which can be used to hide the scammer’s real location and even impersonate the phone numbers of trusted organizations. Last year, for example, clients of the Ritz London hotel had their personal details stolen during a breach at the luxury hotel and the scammers then used the data to mount convincing social engineering attacks against the victims, spoofing the hotel’s official number in the process.
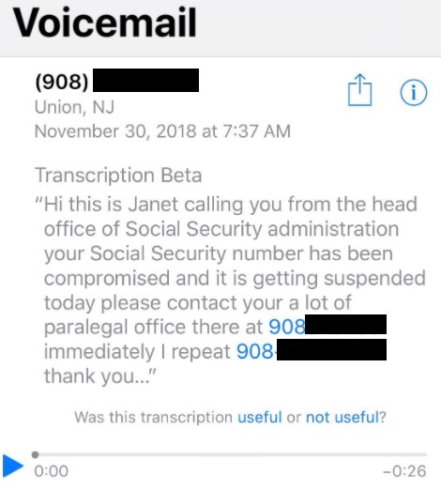
- Multi-channel scams that might start with a smishing text message, a phishing email or a voicemail and encourage the user to call a number. Doing so will put the victim through direct to a scammer.
- Social media scraping and open source research which can provide the scammer with a wealth of information on their victims. It can be used to target specific individuals (say, corporate employees with privileged accounts) and to add legitimacy to the scam – i.e. the visher may repeat back some personal details to the victim so that they might divulge more.
The impact of vishing in the workplace
Vishing is most likely in corporate context to be used to steal privileged credentials. The FBI has warned multiple times of such attacks. Back in August 2020, it detailed a sophisticated operation in which cybercriminals researched their targets and then called pretending to be from IT helpdesk. Victims were encouraged to fill in their log-in details at a previously registered phishing site designed to spoof the company’s VPN log-in page. These credentials were then used to access company databases for customers’ personal information.
Such attacks are more commonplace partly thanks to the mass shift to remote working during the pandemic, the FBI warned. In fact, it was forced to issue another alert in January 2021 for an operation in which similar techniques were used to gain corporate network access.
A now-infamous breach at Twitter, in which highly targeted employees were tricked by vishers into revealing their logins, illustrates that even tech-savvy companies and users can fall victim. In this case, access was used to hijack the accounts of celebrity users to distribute a cryptocurrency scam.
How voice phishing can hit my family
Unfortunately, vishing scammers are also out in force to target consumers. In these attacks, the ultimate goal is to make money from you: either by stealing bank account or card information direct, or tricking you into handing over personal information and logins they can use to access these accounts.
Here are a few typical scams:
Tech support scams
In tech support fraud, victims are often cold-called by someone pretending to be their ISP, or a well-known software or hardware vendor. They’ll claim to have found a non-existent problem with your PC and then elicit payment (and your card details) to fix it, sometimes downloading malware in the process. These scams may also begin with a user presented with a pop-up window that urges them to call a hotline number.
Wardialing
This is the practice of sending automated voicemail messages to large numbers of victims, and usually tries to scare them into calling back—for example by claiming they have tax bills or other fines unpaid.
Telemarketing
Another popular tactic is to call up claiming the recipient has won a fabulous prize. The only catch is that there’s an upfront fee required before the victim can receive their prize.
Phishing/smishing
As mentioned, scams can begin with a spoofed email or fake SMS, encouraging the user to call a number. A popular one is an ‘Amazon’ email claiming something is wrong with a recent order. Calling the number will put the victim on the line with a vishing fraudster.
How to prevent vishing
Although some of these scams are becoming increasingly sophisticated, there’s plenty you can do to mitigate the risk of falling victim. Some basic steps include:
- Go ex-directory, so your number is not publicly available.
- Do not enter your phone number into any online forms (i.e. when buying online).
- Be wary of requests for your bank, personal or any other sensitive information over the phone.
- Exercise caution – don’t engage with any unsolicited callers, especially if they ask to confirm sensitive details.
- Never call back a number left via voicemail. Always contact the organization direct.
- Use multi-factor authentication (MFA) on all online accounts.
- Ensure your email/web security is updated and includes anti-phishing capabilities.